Advancements in technology are a double-edged sword. As technology advances and discoveries are made, so do weaknesses in an organization’s web applications, networks, and software applications. And, of course, new vulnerabilities mean new attack vectors for bad actors. It is, therefore, up to an organization’s security team to find, fix, and/or monitor these vulnerabilities before the attackers do. The vulnerabilities themselves happen for a number of reasons: poorly designed architecture, certain misconfigurations, insecure code, etc. They are often introduced accidentally during the implementation phase of software development. The most common vulnerabilities include software bugs, configuration errors, and design errors, to name a few. To uncover these vulnerabilities, organizations should frequently carry out penetration testing by testing and identifying all the present security risks.
Penetration Testing is carried out through two techniques, automated penetration testing and manual penetration testing. This post will explore automated testing.
What is automated penetration testing?
Automated penetration testing involves using automated tools to scan the vulnerabilities within an organization’s network. Manual tests are expensive, and they often take more time than an organization might have. Automated testing, by comparison, is cheaper and faster (sometimes taking only a few hours, rather than a few weeks). Automated penetration tests have 5 phases: Automated Reconnaissance
Automated Fingerprinting and Scanning, Automated Attack and Exploitation, Automated Post-Exploitation and Lateral Movement and Automated Reporting – of course, designed to function the same way as the traditional red team penetration testing – which continuously launches simulated attacks against a company’s defenses and identifies whatever vulnerabilities it might find. Once the security gaps are discovered, the Automated Penetration Testing platform then provides remediation guidance.
Manual Penetration Testing vs. Automated Penetration Testing
What are the types of Automated Penetration Testing?
Automated Reconnaissance Penetration Testing
Automated Reconnaissance Penetration Testing is a passive test that detects security vulnerabilities and critical issues that exist on the very front-end of an organization (such as an employee’s breached email account). Just like its manual counterpart, the Reconnaissance phase of pentesting is simply meant to gather information in the hopes of finding a loophole or easily exploitable entry point.
Automated External Penetration Testing
Automated External Infrastructure Penetration Testing detects and verifies security weaknesses and critical risks for the publicly-accessible infrastructure. With a powerful combination of active attacks and automated reconnaissance, security teams can find and remediate public-facing risks.
Automated Internal Penetration Testing
Automated Internal Infrastructure Penetration Testing allows you to run internal pentests across corporate networks – on-demand – from any location within public clouds and on-premise data centers, including Azure and AWS. It helps to minimize the time it takes to detect and verify security weaknesses and internal risks.
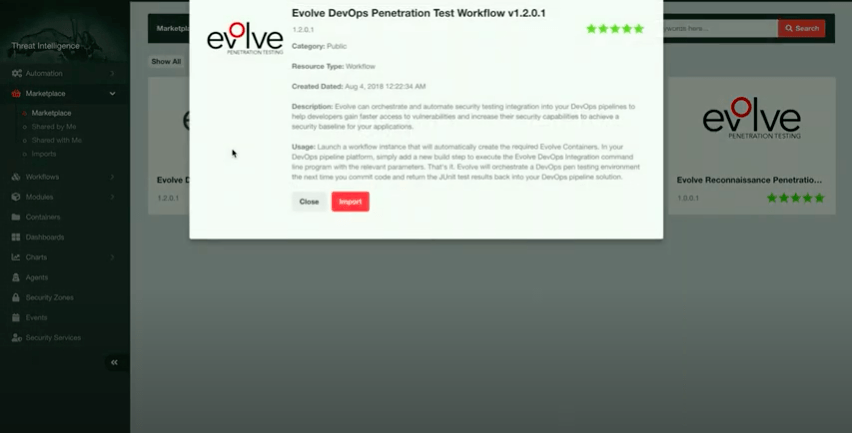
Automated DevOps Application Penetration Testing
Automated DevOps Application Security Testing helps integrate security testing into an organization’s DevOps pipeline. For every code deployment, automated DevOps application testing helps developers discover application-layer vulnerabilities early in the process, saving time, frustration, and – potentially – problems later down the road.
What is the penetration testing process?
There are four penetration testing methods, which can be categorized as follows:
Data collection
There are many data collection tools available for free, not the least of which is Google. Whether the tester is using Google to enumerate employees, or using Nmap to map the network, the tools available can give you a wealth of information including the hardware used, software versions, DB versions and the third-party plugin used in a system.
Vulnerability assessment
Based on the data collected, you can then begin to search for security vulnerabilities. For example, earlier versions of WordPress (before 5.2.3) did not properly filter comments, allowing for SQL injections and XSS. Once existing vulnerabilities are discovered, the pentesters can then launch attacks through the identified entry points.
Exploitation
Here is where the actual attacks occur. In the above example, the pentester may execute a SQL injection, or open a backdoor into the database.
Report preparation and result in analysis
After all the tests have been completed, the pentester prepares a detailed report to make corrective actions. The report lists all the vulnerabilities that were identified together with recommendations for remediation.
Benefits of Automated Penetration Testing
Increased Speed and Efficiency
Automated penetration testing tools can conduct thorough scans much faster than manual testing, often completing in hours what might take a human team weeks. This rapid turnaround is helps to maintain security in fast-paced environments.
Consistency and Repeatability
Automation ensures that tests are conducted consistently every time, reducing the risk of human error and ensuring that the same thorough checks are performed with each test.
Scalability
Automated tools can easily scale to cover extensive networks and large numbers of applications, making them ideal for large organizations with complex IT infrastructures.
Cost-effectiveness
By reducing the need for extensive manual labor, automated penetration testing can significantly cut costs while still providing comprehensive security assessments.
Vulnerability Scanning vs Automated Penetration Testing
Automated penetration testing offers the following key benefits over vulnerability scanning:
Visibility
A penetration test provides a deeper understanding of your environment and how it can be exploited by an attacker. While a vulnerability scan can identify known vulnerabilities, a pen test simulates real-world attacks to exploit weaknesses, providing a comprehensive view of your security posture.
Context
Penetration testing offers valuable context, demonstrating how an attacker could leverage vulnerabilities to gain access to systems or data. This helps prioritize which vulnerabilities to address first based on their real-world impact.
Real-world Risk Approach
Penetration testing considers not just technical vulnerabilities but also the people, processes, and physical security measures that could be exploited, offering a holistic view of your security posture.
Depth of Analysis
Vulnerability scanning typically identifies potential vulnerabilities, while automated penetration testing goes further by actively exploiting these vulnerabilities to assess their impact.
Identification of False Positives and False Negatives
Automated penetration testing tools are designed to minimize false positives and false negatives by validating findings through active exploitation. Discover how these tools do this in our blog post.
Coverage of Complex Vulnerabilities
Automated penetration testing can uncover complex vulnerabilities that may be missed by simpler vulnerability scans.
Adaptability to Evolving Threat Landscape
Automated penetration testing tools are continuously updated to address new and emerging threats, ensuring that they remain effective against the latest attack vectors.
Integration with Remediation Efforts
Automated tools often provide detailed remediation guidance, helping organizations to quickly and effectively address identified vulnerabilities.
Why Choose Automated Penetration over Vulnerability Scanning?
While vulnerability scanners are useful for identifying known vulnerabilities, prioritizing fixes, and tracking progress, they have limitations. A vulnerability scanner will tell you what holes are in your systems and how to fix them. However, it can't tell you who might be trying to exploit your data, how they might be doing it, what vulnerabilities they'll target, and what happens when they do.
Furthermore, vulnerability scans often focus on individual systems or applications without considering how they interconnect. For instance, a vulnerability in an internet-facing web application combined with a weak authentication mechanism on an internal system can create a significant attack pathway. Vulnerability scans cannot chain multiple vulnerabilities to understand the true impact of a breach, which is critical for comprehensively securing your infrastructure.
In contrast, penetration testing identifies holes in your systems and explores how they could be abused to create larger attacks, providing a much deeper understanding of your environment and how it can be exploited.
Learn more about why pen testing is the best approach for your organization here.
EvolvePT - Your Automated Pen Testing Tool
Evolve
secures both internal and external applications and systems in an organization, and allows you to execute on-demand automated pen-testing across an organization’s systems. Evolve even offers monitoring of an organization’s domain names and email addresses. To date, there have been over 700 billion compromised accounts, whether email, health sites, or e-commerce sites. Evolve will protect and monitor your corporate accounts from sites whose credentials may have been breached, helping to keep your business from being added to that statistic. Check out the benefits you can get with EvolvePT:
- On-Demand Testing: Schedule tests anytime, anywhere, at your convenience with 24/7 penetration testing services.
- Deep Visibility: Comprehensive assessment of every possible attack scenario, including organizational reconnaissance, man-in-the-middle attacks, automated exploitation, privilege escalation, and lateral movement across both cloud environments and your organization’s security zones.
- Prioritized Remediation: Focus on the biggest threats first with prioritized remediation recommendations from expert security analysts.
- Automation: Automate repetitive and time-consuming tasks, reducing human error and allowing your security team to focus on strategic initiatives.
- Real-World Risk Assessment: Test your network against the latest threats to ensure a secure foundation for your projects.
- Location-Agnostic Testing: Protect your data no matter where it’s stored with EvolvePT's flexible testing capabilities.
- Detailed Reporting: Get comprehensive reports with insights into vulnerabilities, including network and software vulnerabilities, email security issues, and more. Understand the interconnected risks across your infrastructure.
Ready to boost your vulnerability management with EvolvePT? Book a demo today to see how EvolvePT can enhance your security posture and keep your organization safe from evolving threats.
Conclusion
Automated Penetration Testing, when used in conjunction with regularly scheduled manual tests and standard detection tools, can provide a much more efficient and effective security position. It’s high time to consider reaping the benefits of automated breach simulation by moving beyond the limitations of point-in-time testing.