As recent cyberattacks against companies and governments have demonstrated, no organization is safe from cybercrime. Moreover, security incidents and data breaches are becoming expensive, costing a staggering
$3.86 million
on average. It is clear that prevention is, now more than ever, a necessary focus.
To prevent malicious attacks, enterprises need strong cybersecurity programs with constant vigilance, threat detection, and remediation. However, these objectives are difficult to achieve with a strictly human-based approach. This is due to the prevalent problem of alert fatigue, a combination of sheer volume (large amounts of data) and wasted time (mostly in the form of large amounts of false positives). Security automation can help minimize this problem, strengthening an organization’s security posture while also aiding the security team’s day-to-day responsibilities. Here’s how.
What is Security Automation?
According to recent research, 70% of IT leaders say that security alert volume has more than doubled since 2015. Moreover, 83% believe that their security teams experience alert fatigue. To address the issue, security personnel either increase the alert thresholds (therefore reducing volume), or simply ignore certain alert categories. With either approach, genuine alerts often get lost in the noise, which can be disastrous in today’s expanding threat landscape. While it would seem, therefore, prudent to expand the employee pool, hiring more human resources is not always feasible. Here’s where security automation can be very valuable.
Security automation replaces manual incident response processes, such as scanning, detection, investigation and remediation, allowing SecOps teams to respond more efficiently to threats. A security automation tool minimizes the need for human intervention to identify incoming threats and prioritize alerts. It instantly engages with an incident, quickly responds to alerts, and contains and resolves issues.
What are the Benefits of Security Automation?
Enhanced security capabilities
With security automation, the organization’s Security Operations Center (SOC) can reduce false-positive alerts, reduce MTTR, and increase MTBF. They can also conduct deeper analyses and implement more proactive security measures, strengthening the organization’s capability to withstand threats.
Optimized security budget and higher ROI
Security automation empowers security teams to move away from routine detection and response tasks, and focus on more value-added work (like advanced threat defense).
Fewer errors for stronger threat detection and incident response
Intelligent security automation “learns” from patterns, and standardizes threat detection and incident response. This allows for better protection, minimizes errors, and improves the accuracy of alert investigations.
In addition, security automation tools can also:
- Determine legitimate alerts for deeper investigation
- Triage and mitigate potential risks by following the organization’s decision-making workflow
- Standardize incident response processes to reduce response times
- Streamline communications between security and other teams
- Increase visibility of security metrics for a stronger cybersecurity posture
The Evolution of Security Automation
From automated penetration testing to streamlined security queues, security automation has evolved into a more holistic approach where human intervention is not required. Today, the focus is increasingly on Orchestration, Automation and Response.
What is Security Orchestration, Automation and Response?
Security Orchestration, Automation and Response (SOAR) combines automated data gathering, case management, analytics, and security automation, so organizations can easily implement more sophisticated defense-in-depth capabilities to protect themselves. While
security automation
is about replacing manual incident response tasks with automation,
security orchestration
is about integrating disparate security tools and platforms to enable automated, machine-speed decision-making. It centralizes security operations data from different sources into a single interface, so security teams can quickly understand the threat
landscape
and respond appropriately.
What that means is the threat is placed within the overall context of the network and organization. It is difficult to make an informed decision without information, and Orchestration helps provide that information.
How to Get Started with Security Automation
To get the most value out of security automation, it’s important to first establish security needs and objectives, define relevant use cases, study other security automation examples, and research providers.
Establish security objectives
In addition to improving their threat detection and remediation capability, organizations may also have other specific security goals: reduce alert fatigue, minimize inefficiencies, make operations leaner, etc. It’s important to identify these goals before implementing a security automation system.
Define use cases and examples
The enterprise lists the ways they will use security automation. It helps to review other security automation examples for inspiration and information.
Research providers
While researching providers, it’s useful to ask these questions:
- Is their platform “no-code” for easy deployment and use?
- Is it customizable and scalable?
- Does it provide third-party integrations and plugins?
- Can they provide security automation examples from previous deployments?
- Is staff training required?
- Is technical support available?
The best security automation systems offer:
- Standardized incident response workflows
- Pre-built and customizable playbooks based on internal rules
- Integration with other security systems, like SIEMs, firewalls, and endpoint solutions
WHAT ARE THE SIGNS THAT AN ORGANIZATION NEEDS SECURITY AUTOMATION?
SECURITY TEAM OVERLOAD
Security teams, who are already understaffed, are overwhelmed by the sheer volume of security alerts, dozens of tools to manage, and false positives. In addition, they end up wasting time on repetitive tasks. As a result, many alerts slip through the cracks, leaving the organization prone to security breaches.
MEET COMPLIANCE REQUIREMENTS
A developing business requires more complex infrastructures and technology stacks that are constantly evolving in unexpected ways. With automation, organizations can eliminate much of the manual, administrative work from compliance activities and scale its activities and resources to meet growing compliance needs. Compliance can expand with the company without risking the security of protected information assets.
DELAYED RESPONSE
Since security analysts can only investigate a small portion of the alerts that arrive, it is difficult if and very rare for them to respond in real time. The incident response time lags as a result. Automation tools and solutions enable security teams to resolve incidents more quickly, reducing the total time spent per incident.
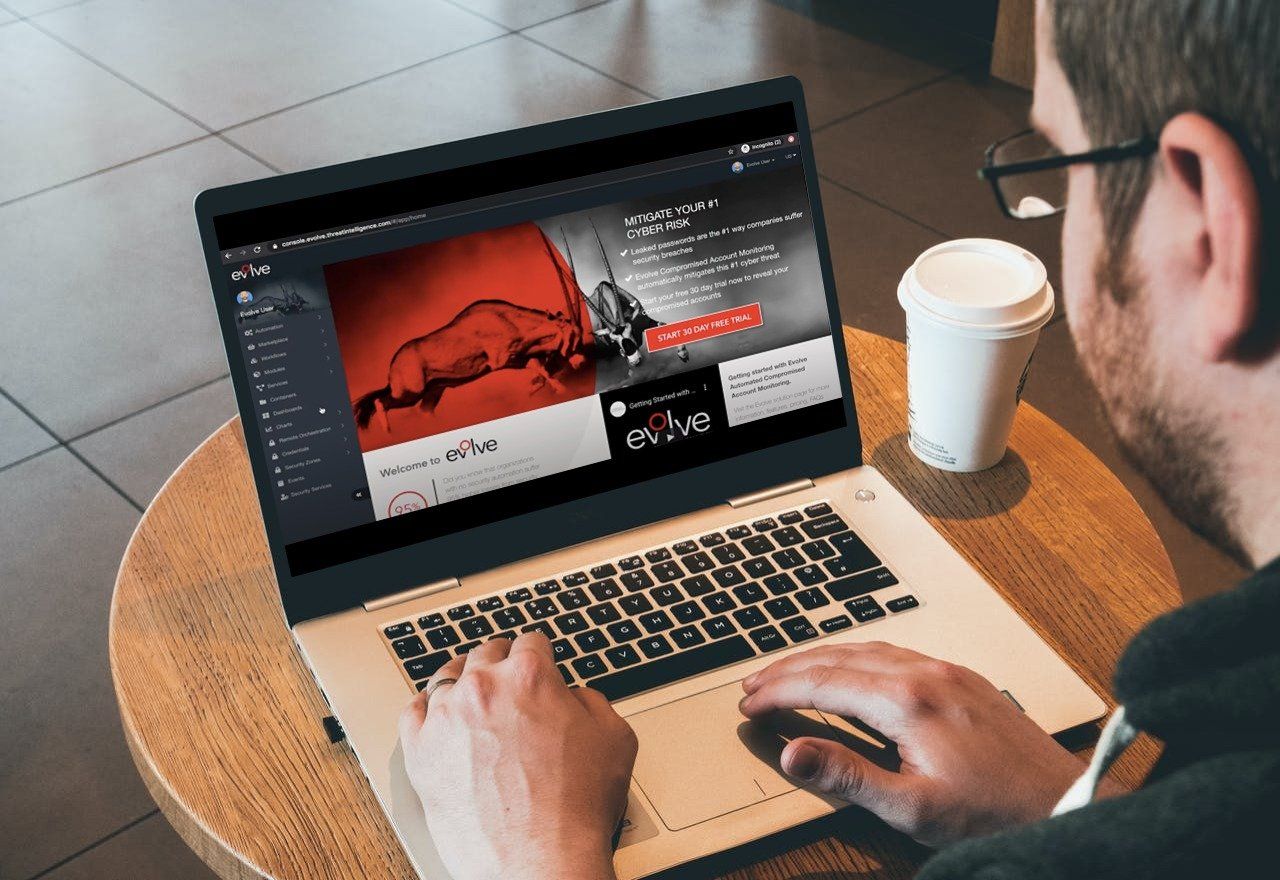
Evolve: The World’s First Dedicated Security Automation Cloud
Getting started with Evolve is easy and fast it is:
Step 1: Register an Evolve Account
Step 2: Navigate to the Evolve Marketplace
Step 3: Import the Automated External Penetration Test workflow into your account
Step 4: Click to launch a workflow instance to start running a test
Step 5: Done! Evolve does all the work to secure your business!